Loading...
You should use the new WormNAT2 module instead, which comes with WormKit.
WormNAT
What is WormNAT?
WormNAT is a program for Worms: Armageddon that allows you to host on-line WormNET games, even if you are behind NAT, a misconfigured router or firewall. You will also need this program to play games hosted with WormNAT.
WormNAT places itself between Worms: Armageddon and your Internet connection. It intercepts game connections and routes them through a 3rd-party server. The connection parameters are transmitted via WormNET, afterwards all players connect to the same server which routes the data.
Currently there are two methods (protocols) for routing data - IRC and SOCKS.
How to get up and running
This step-by-step walkthrough describes how to configure WormNAT to host using the SOCKS protocol, which is the preferred method.
- Download WormNAT, and unpack the ZIP to the directory where you installed Worms: Armageddon.
- Run WormNATConfig.exe.
- Set Hosting mode to SOCKS.
- Click on the Automatic configuration button. Have patience, this could take some time.
- When the auto-configuration has successfully finished, click OK.
- From now on, to play on-line using WormNAT you will need to launch WormNAT.exe instead of the usual WA.exe. Consider updating your desktop shortcuts.
If you can host games without WormNAT, uncheck Enable WormNAT hosting in the configuration utility. Since the connection parameters are retrieved from the hosting player, your network settings are ignored.
WormNAT will not interfere with normal WormNET games. You will still be able to join, and if you have disabled WormNAT hosting, host normal WormNET games.
Note: When you are creating or joining a WormNAT game, Worms may appear to freeze for about 10-20 seconds. This is to be expected - during this time WormNAT retrieves the connection parameters and creates the routed connection.
Configuration
You can configure WormNAT with the configuration utility WormNATConfig.exe, or by directly editing the INI file. We'll describe the former method.
Common options:
- Enable WormNAT hosting
You should only enable this option if you can't normally host. Enabling this option instructs WormNAT to intercept your attempts to host a game and create WormNAT-hosted games (people who aren't using WormNAT will be unable to join your game).
If you only need WormNAT to play with other people hosting games using WormNAT, uncheck this and you are done - since the connection parameters are retrieved from the hosting player, the rest of the configuration is ignored.
You will be able to join normal WormNET games indifferently of this setting. - Loopback port
WormNAT will use this port for internal data flow. Any un-used port will do. - Hosting mode
The back-end module for routing data.
IRC is usually more fail-prone but laggy (it gets much more laggier the more players join), and has a very limited data transfer rate (never attempt to load a full-color PNG map through IRC!). The IRC back-end was created mostly as an experiment.
SOCKS is more preferred, thou public SOCKS servers get removed with time (and you have to re-run the auto-configuration when that happens). If you can set up your own SOCKS server that supports BIND, that would be perfect (just make sure you restrict the list of allowed IPs or anyone will be able to use your proxy).
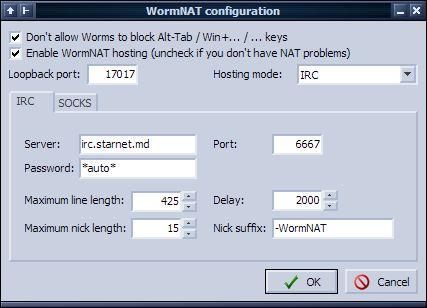
Settings for IRC:
- Server / Port
The server/port to your IRC server of choice. - Password
If your IRC server requires a password, set it here. Use *auto* if you plan to use the WormNET IRC server. - Maximum line length:
The maximum length of messages the IRC server accepts, in characters. Leave about 5-10% overhead. - Maximum nick length:
The maximum length of nicknames that users are allowed to have on the server. - Delay:
The minimum time (in milliseconds) between each line of encoded data sent to the server. Lower values mean less lag, however consider that most servers manually throttle your messages which can lead to incremental lag, and too low values will get you kicked for excess flood. - Nick suffix:
In order to avoid collision with your usual nick on the IRC server, the WormNAT IRC client appends a suffix to your WormNET nickname - which you can set here. It may overlap the last few characters of your nickname (for example: WormNET nick is CyberShadow, suffix is -WormNAT and max nick length=15 ⇒ WormNAT nickname will be CyberSh-WormNAT).
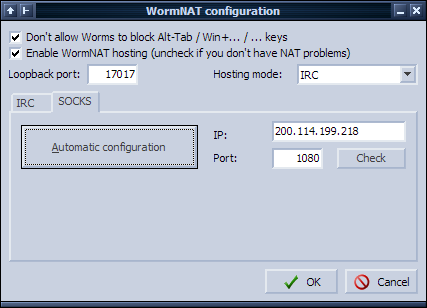
Settings for SOCKS:
Please note that not any SOCKS server will do. WormNAT can work only with SOCKS4-compatible servers that support the BIND command and are configured correctly. You can use the Check button to verify if WormNAT can work with a specified SOCKS server.
- IP / Port
The IP/port to the SOCKS server. - Automatic configuration
Clicking this button will make the WormNAT configuration utility download a list of free SOCKS proxies and scan them to find an usable proxy. You can check the scan details in the log text-box (not visible in the screenshot). In the case it will find an usable proxy, it will automatically fill out the IP/Port values. - Check
Click it to check if the entered proxy is properly set up and compatible with WormNAT.
Note: for SOCKS to work, you will need to configure your external address in the WormNET configuration (or leave it blank if you wish WormNET to detect it). This is needed because the SOCKS server needs to know from what IP to expect an incoming connection on the bound port.
How it works
WormNET
Before you try to understand how WormNAT works, you should at least have some knowledge of WormNET's structure.
A WormNET server is basically composed of a slightly (if at all) modified IRC server and an HTTP server with a few scripts. As of writing this page, WormNET is running 2.8/hybrid-6.3.1(20020418_1) and Apache/2.0.54 + PHP/4.3.10-16 on Debian GNU/Linux.
So, the typical screen you see in a WormNET channel is actually made up of two logical parts:
- The first is the game list, which lists all games in the "waiting for players" state; WormNET games are managed by the PHP scripts.
- The second is the nickname list and the chatter area, which are managed through IRC.
These parts aren't really interconnected - thus, it's possible to create a game without connecting to the IRC server, and it is possible to connect to the IRC server without logging in through the web interface (this might change with time).
A typical connection sequence to WormNET is as following:
- Worms retrieves Login.asp, which contains a <CONNECT> directive - the IP/Port to the IRC server.
- Worms logs on the IRC server, and gets the list of channels.
- when the player joins a channel, Worms retrieves the channel scheme and game list for the channel (RequestChannelScheme.asp, GameList.asp).
The game list is periodically automatically updated. - when a player hosts a game, Worms sends a "create game" request via Game.asp; when the actual game starts (no more people can join) or when the host exits before the game starts, a similar "close game" request is sent.
- when a player hosts or enters a game, he is disconnected from IRC.
- when a player exits a game, he must reconnect to WormNET from the beginning.
WormNAT
WormNAT intercepts almost all WormNET-related traffic, and modifies it as it passes between Worms and WormNET.
First of all, WormNAT intercepts game creation (hosting) commands. It substitutes your address (as it is configured in
Worms' network options) with the URL to the WormNAT homepage, which will be visible to players who do not have WormNAT.
This is needed so WormNAT will distinguish normal games and WormNAT games.
Secondly, WormNAT does not allow Worms to disconnect the player from IRC when he is hosting a game - instead it "takes over"
the connection (thou it doesn't stop Worms parting from any joined channels first). This is necessary to communicate the connection
parameters to players who wish to join the game.
When a player (with WormNAT) tries to join the aforementioned game, WormNAT queries the host player for the connection parameters. After those are received, WormNAT connects to the server configured by the host and creates the back-end connection.
IRC
WormNAT connects to the IRC server (which might not necessarily be the WormNET IRC server), using a modified version of the player's WormNET nickname (see the configuration page). The client then communicates with the host via NOTICE messages; binary data that is sent between the games is packed and encoded into printable characters before being transmitted over IRC.
The users don't join any channels, nor is it necessary; all nicknames are calculated with the same algorithm, and a copy of data is sent to each player by the game host.
SOCKS
WormNAT uses the BIND command of SOCKS servers. By far not all SOCKS servers are configured correctly for BIND commands; that's why an automatic configuration utility was written.
For each player, the server connects to the SOCKS proxy and requests a BIND; the proxy replies with the port to which it is listening for an incoming connection. The server then sends that port as part of the network configuration to the client via WormNET IRC, after which the client proceeds to connect to that port, thus establishing the link.
You can get more detail on the inner workings of WormNAT by examining the log file (WormNAT.log).
Source code
I have included the full Delphi source code for WormNAT. You will need madCollection to recompile the core DLLs.
Download
WormNAT is now distributed as a WormKit module; see the WormKit homepage for more information.
Credits
WormNAT started out as a quick hack / experiment so I could play with my friend (we both couldn't host at the time), but my network
administrator gave in to my never-ending pleads to forward the required ports before I could finish the program.
I haven't touched it since then for some time, until I decided to finish the project - more as an exercise in networking, hooking and
data-tunneling, then for any personal gain. And here we are :)
Thanks to ViruX, for giving me the idea to implement a SOCKS BIND back-end.
Thanks to Spiker, Alexis, Bughish and RUN for testing and support.
Thanks to Team17 for the game, and Deadcode for the updates;
perhaps one day, thanks to him, we won't need programs like this one at all ;)
The author of this program is Vladimir Panteleev (aka The_CyberShadow). Contact me by .
